Checking Out the Function of Universal Cloud Storage Space Solutions in Information Defense and Conformity
In today's digital landscape, the utilization of global cloud storage space services has actually come to be paramount in attending to information security and conformity requirements for companies throughout various sectors. As businesses increasingly depend on cloud storage remedies to handle and guard their information, discovering the elaborate role these services play in making certain data safety and conference regulative standards is important. From mitigating threats to boosting data accessibility, cloud storage solutions use a complex technique to securing delicate info. The evolving nature of cyber hazards and governing frameworks offers a vibrant obstacle that companies need to browse properly to promote their information security and compliance mandates. By delving into the nuances of universal cloud storage solutions, a clearer understanding of their influence on data protection and governing conformity arises, shedding light on the intricacies and opportunities that exist in advance.
Importance of Cloud Storage Provider
Cloud storage services play a critical function in modern-day information administration approaches due to their scalability, access, and cost-effectiveness. Scalability is a key advantage of cloud storage space, allowing organizations to easily readjust their storage space capacity as information needs rise and fall.
Availability is an additional essential facet of cloud storage solutions. By saving data in the cloud, customers can access their information from anywhere with a web link, helping with partnership and remote work. This ease of access advertises functional performance and allows smooth sharing of information throughout teams and places.
Additionally, the cost-effectiveness of cloud storage services can not be downplayed. By leveraging cloud storage space, businesses can lower expenses related to getting and keeping physical servers. universal cloud storage. Furthermore, lots of cloud storage carriers offer pay-as-you-go prices designs, allowing companies to pay only for the storage capability they utilize. On the whole, the relevance of cloud storage solutions lies in their ability to enhance information management processes, boost accessibility, and reduced operational costs.
Data Security Techniques With Cloud
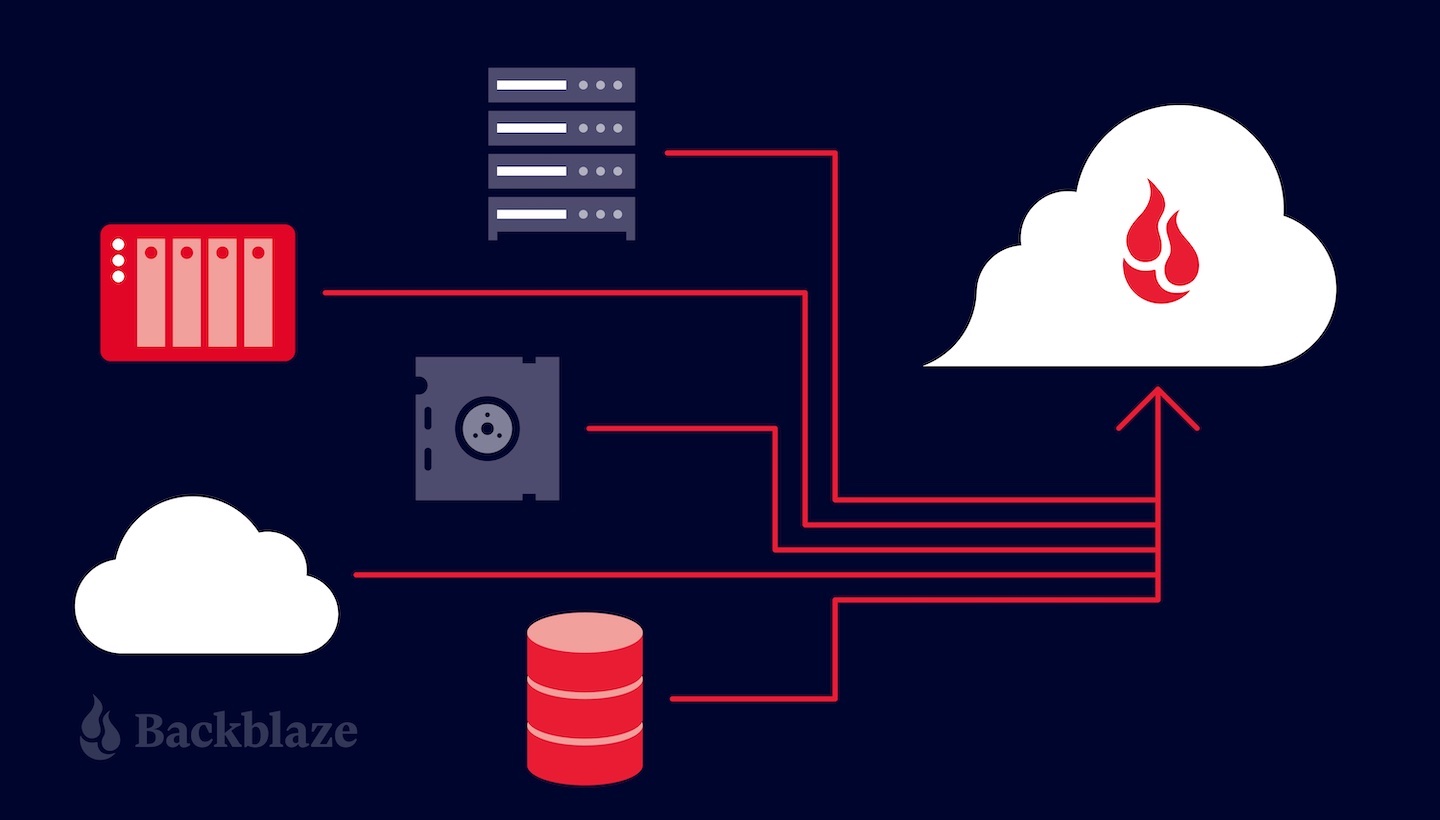
Carrying out robust information security procedures is essential for making sure the safety and security and discretion of info kept in cloud environments. Encryption plays a vital function in safeguarding data both en route and at remainder. By securing data prior to it is uploaded to the cloud and preserving control over the file encryption tricks, organizations can protect against unapproved gain access to and mitigate the threat of data breaches. Additionally, implementing accessibility controls and authentication devices aids in managing who can access the information kept in the cloud. Multi-factor authentication, strong password plans, and routine gain access to evaluations are some techniques that can improve information protection in cloud storage services.
Routinely backing up information is one more crucial element of data protection in the cloud. By producing backups saved in different areas, companies can make sure information schedule and strength in instance of unanticipated events such as cyber-attacks, hardware failings, or natural disasters. Performing normal security audits and analyses can help identify vulnerabilities and make certain conformity with data defense regulations. By incorporating security, access controls, backups, and regular safety evaluations, companies can develop a durable data security method in cloud settings.
Conformity Factors To Consider in Cloud Storage Space
Offered the critical nature of information protection methods in cloud settings, companies need to also prioritize conformity factors to consider when it comes to storing data in the cloud. When using cloud storage space services, businesses need to ensure that the supplier conforms with industry-specific criteria such as GDPR, HIPAA, or PCI DSS, depending on the kind of data being stored.

Challenges and Solutions in Cloud Safety
Making certain durable safety procedures in cloud environments presents a complex difficulty for companies today. Among the main obstacles in cloud security is data violations. Malicious stars frequently target cloud systems to acquire unauthorized access to delicate information. To minimize this danger, organizations should carry out strong security procedures, accessibility controls, and routine protection audits. An additional obstacle is the shared duty model in cloud computing, where both the cloud provider and the customer are liable for different aspects of security. This can result in complication and voids in protection insurance coverage if not clearly specified. Organizations has to clearly lay out duties and duties to make certain extensive security procedures are in place.
Future Patterns in Cloud Information Protection
The developing landscape of cloud data security is marked by a growing emphasis on aggressive protection techniques and flexible safety and security procedures (universal cloud storage). As innovation developments and cyber risks end up being a lot more innovative, organizations are significantly focusing on anticipating analytics, man-made knowledge, and device learning to enhance their information defense capabilities in the cloud
One of the future trends in cloud data protection is the integration of automation and orchestration tools to improve security procedures and response processes. By automating regular tasks such as hazard detection, case reaction, and patch management, companies can improve their overall safety posture and better shield Recommended Reading their data in the cloud.
In addition, the adoption of a zero-trust safety version is obtaining grip in the realm of cloud data protection. This approach thinks that risks can be both outside and inner, calling for continual authentication and permission for all customers and gadgets accessing the cloud environment. By implementing a zero-trust structure, organizations can minimize the danger of data violations and unauthorized accessibility to delicate info stored in the cloud.
Verdict